The U.S. Cybersecurity and Infrastructure Security Agency is warning of active exploitation attempts that leverage the latest line of “ProxyShell” Microsoft Exchange vulnerabilities that were patched earlier this May, including deploying LockFile ransomware on compromised systems.
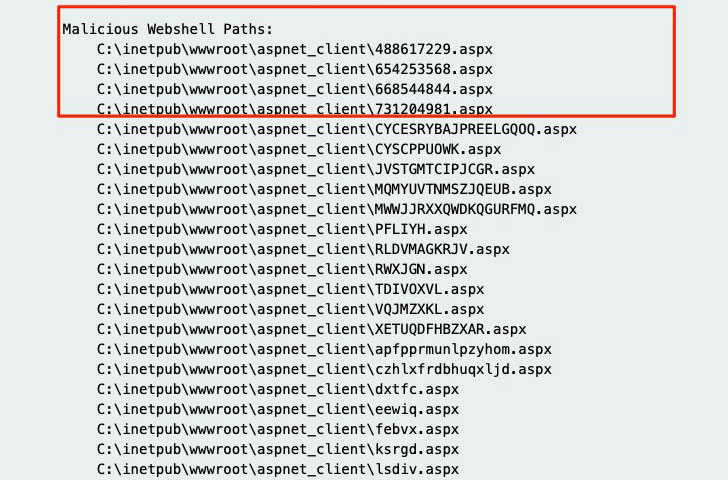
Tracked as CVE-2021-34473, CVE-2021-34523, and CVE-2021-31207, the vulnerabilities enable adversaries to bypass ACL controls, elevate privileges on the Exchange PowerShell backend, effectively permitting the attacker to perform unauthenticated, remote code execution. While the former two were addressed by Microsoft on April 13, a patch for CVE-2021-31207 was shipped as part of the Windows maker’s May Patch Tuesday updates.

“An attacker exploiting these vulnerabilities could execute arbitrary code on a vulnerable machine,” CISA said.
The development comes a little over a week after cybersecurity researchers sounded the alarm on opportunistic scanning and exploitation of unpatched Exchange servers by leveraging the ProxyShell attack chain.
Originally demonstrated at the Pwn2Own hacking contest in April this year, ProxyShell is part of a broader trio of exploit chains discovered by DEVCORE security…
http://feedproxy.google.com/~r/TheHackersNews/~3/ZBrnqEFoZ70/microsoft-exchange-under-attack-with.html