Cybersecurity researchers have disclosed a new backdoor program capable of stealing user login credentials, device information and executing arbitrary commands on Linux systems.
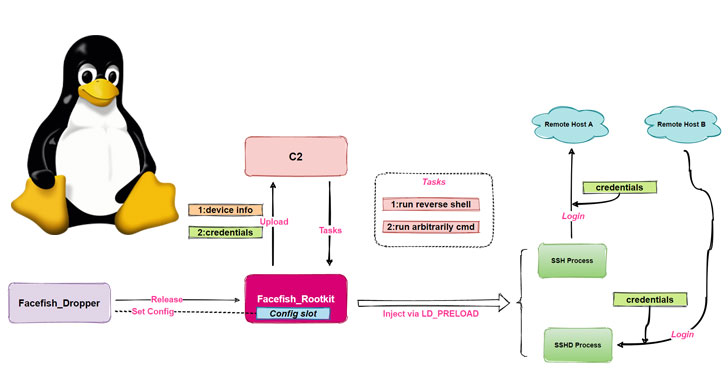
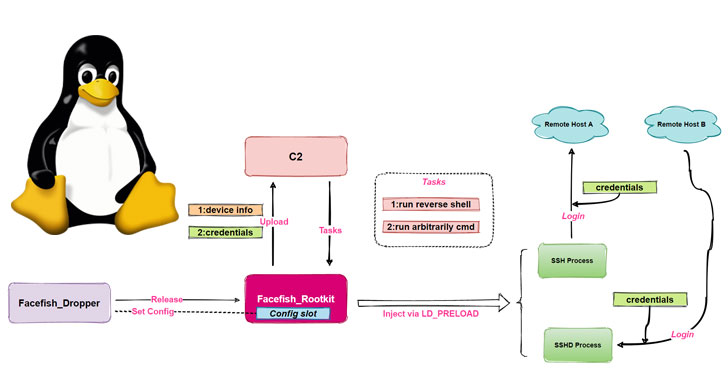
The malware dropper has been dubbed “Facefish” by Qihoo 360 NETLAB team owing its capabilities to deliver different rootkits at different times and the use of Blowfish cipher to encrypt communications to the attacker-controlled server.
“Facefish consists of 2 parts, Dropper and Rootkit, and its main function is determined by the Rootkit module, which works at the Ring 3 layer and is loaded using the LD_PRELOAD feature to steal user login credentials by hooking ssh/sshd program related functions, and it also supports some backdoor functions,” the researchers said.

The NETLAB research builds on a previous analysis published by Juniper Networks on April 26, which documented an attack chain targeting Control Web Panel (CWP, formerly CentOS Web Panel) to inject an SSH implant with data exfiltration capabilities.
Facefish goes through a multi-stage infection process, which commences with a command injection against the CWP to retrieve a dropper (“sshins”) from a remote server, which then releases a rootkit…
http://feedproxy.google.com/~r/TheHackersNews/~3/81J9eSVrKKU/researchers-warn-of-facefish-backdoor.html