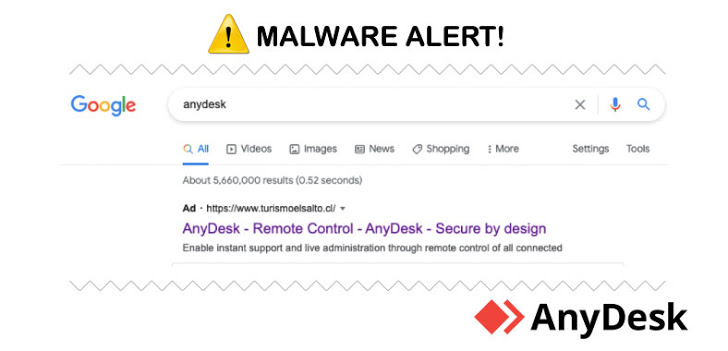
Cybersecurity researchers on Wednesday publicized the disruption of a “clever” malvertising network targeting AnyDesk that delivered a weaponized installer of the remote desktop software via rogue Google ads that appeared in the search engine results pages.
The campaign, which is believed to have begun as early as April 21, 2021, involves a malicious file that masquerades as a setup executable for AnyDesk (AnyDeskSetup.exe), which, upon execution, downloads a PowerShell implant to amass and exfiltrate system information.
“The script had some obfuscation and multiple functions that resembled an implant as well as a hardcoded domain (zoomstatistic[.]com) to ‘POST’ reconnaissance information such as user name, hostname, operating system, IP address and the current process name,” researchers from Crowdstrike said in an analysis.
AnyDesk’s remote desktop access solution has been downloaded by more than 300 million users worldwide, according to the company’s website. Although the cybersecurity firm did not attribute the cyber activity to a specific threat actor or nexus, it suspected it to be a “widespread campaign affecting a wide range of customers” given the large user base.
http://feedproxy.google.com/~r/TheHackersNews/~3/wGoXioXuOOg/malvertising-campaign-on-google.html