A week after the US government issued an advisory about a “global intelligence gathering mission” operated by North Korean state-sponsored hackers, new findings have emerged about the threat group’s spyware capabilities.
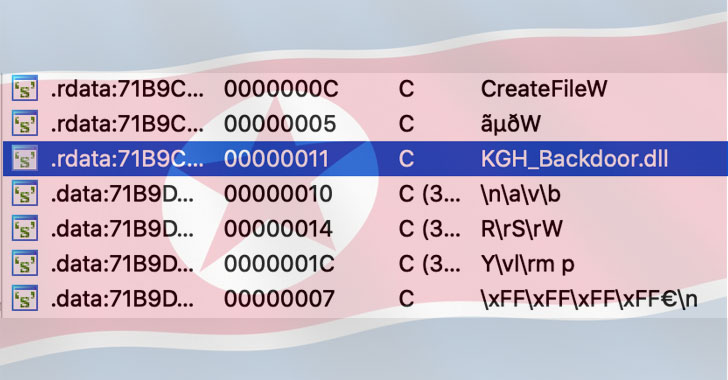
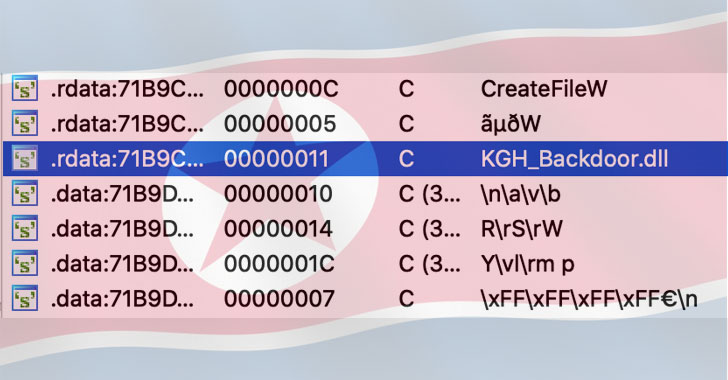
The APT — dubbed “Kimsuky” (aka Black Banshee or Thallium) and believed to be active as early as 2012 — has been now linked to as many as three hitherto undocumented malware, including an information stealer, a tool equipped with malware anti-analysis features, and a new server infrastructure with significant overlaps to its older espionage framework.
“The group has a rich and notorious history of offensive cyber operations around the world, including operations targeting South Korean think tanks, but over the past few years they have expanded their targeting to countries including the United States, Russia and various nations in Europe,” Cybereason researchers said in an analysis yesterday.
Last week, the FBI and departments of Defense and Homeland Security jointly released a memo detailing Kimsuky’s tactics, techniques, and procedures (TTPs).
Leveraging spear-phishing and social engineering tricks to gain the initial access into victim networks, the APT…
http://feedproxy.google.com/~r/TheHackersNews/~3/6uTYoCnRAAw/new-kimsuky-module-makes-north-korean.html