Writing advanced malware for a threat actor requires different groups of people with diverse technical expertise to put them all together. But can the code leave enough clues to reveal the person behind it?
To this effect, cybersecurity researchers on Friday detailed a new methodology to identify exploit authors that use their unique characteristics as a fingerprint to track down other exploits developed by them.
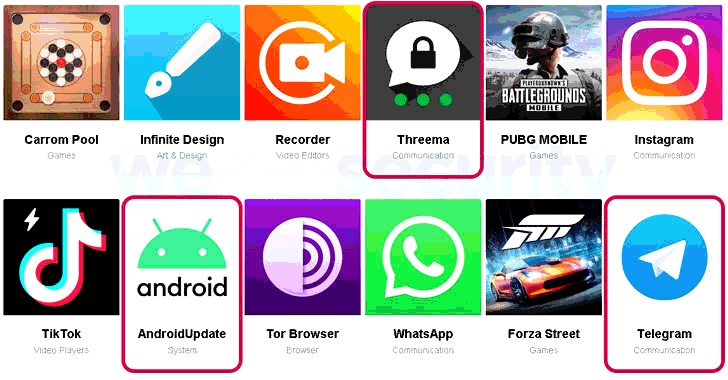
By deploying this technique, the researchers were able to link 16 Windows local privilege escalation (LPE) exploits to two zero-day sellers “Volodya” (previously called “BuggiCorp”) and “PlayBit” (or “luxor2008”).
“Instead of focusing on an entire malware and hunting for new samples of the malware family or actor, we wanted to offer another perspective and decided to concentrate on these few functions that were written by an exploit developer,” Check Point Research’s Itay Cohen and Eyal Itkin noted.
Fingerprinting an Exploit Writer’s Characteristics
The idea, in a nutshell, is to fingerprint an exploit for specific artifacts that can uniquely tie it to a developer. It could be in using hard-coded values, string names, or even how the code is organized and certain…
http://feedproxy.google.com/~r/TheHackersNews/~3/6DRmnaFJT5g/exploit-development.html