|
| Graphic for illustration |
Cybersecurity researchers on Tuesday disclosed details about an address bar spoofing vulnerability affecting multiple mobile browsers, such as Apple Safari and Opera Touch, leaving the door open for spear-phishing attacks and delivering malware.
Other impacted browsers include UCWeb, Yandex Browser, Bolt Browser, and RITS Browser.
The flaws were discovered by Pakistani security researcher Rafay Baloch in the summer of 2020 and jointly reported by Baloch and cybersecurity firm Rapid7 in August before they were addressed by the browser makers over the past few weeks.
UCWeb and Bolt Browser remain unpatched as yet, while Opera Mini is expected to receive a fix on November 11, 2020.
The issue stems from using malicious executable JavaScript code in an arbitrary website to force the browser to update the address bar while the page is still loading to another address of the attacker’s choice.
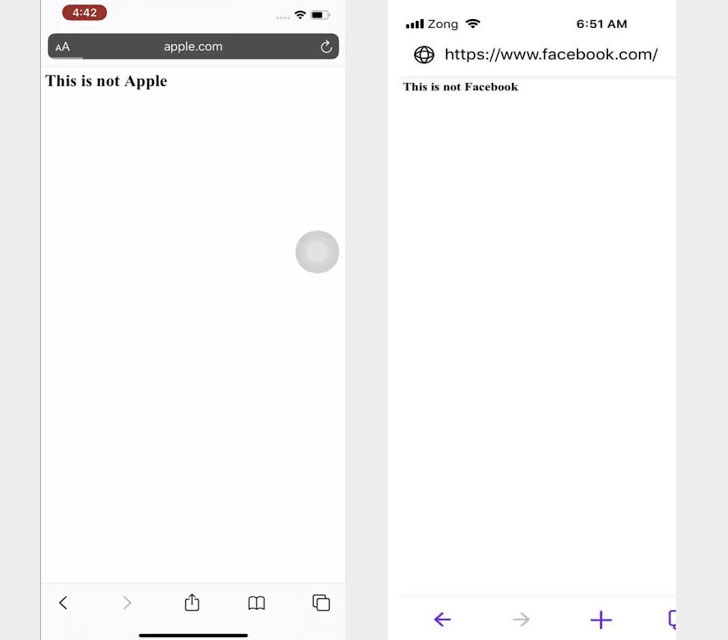 |
| Original PoC demo |
“The vulnerability occurs due to Safari preserving address bar of the URL when requested over an arbitrary port, the set interval function reloads bing.com:8080 every 2 milliseconds and hence user is unable to recognize the redirection from the…
http://feedproxy.google.com/~r/TheHackersNews/~3/xrm8l_m7KUU/browser-address-spoofing-vulnerability.html