In what’s one of the most innovative hacking campaigns, cybercrime gangs are now hiding malicious code implants in the metadata of image files to covertly steal payment card information entered by visitors on the hacked websites.
“We found skimming code hidden within the metadata of an image file (a form of steganography) and surreptitiously loaded by compromised online stores,” Malwarebytes researchers said last week.
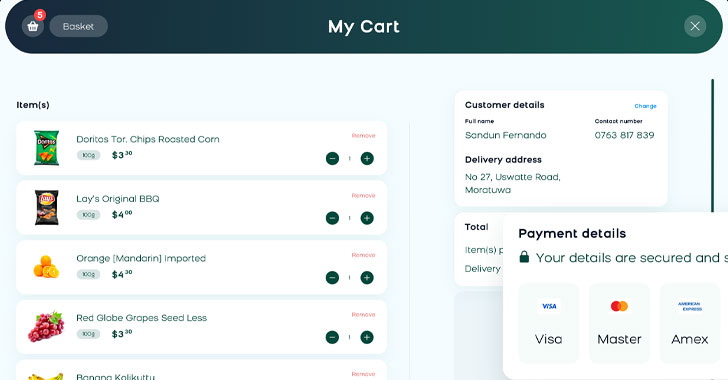
“This scheme would not be complete without yet another interesting variation to exfiltrate stolen credit card data. Once again, criminals used the disguise of an image file to collect their loot.”
The evolving tactic of the operation, widely known as web skimming or a Magecart attack, comes as bad actors are finding different ways to inject JavaScript scripts, including misconfigured AWS S3 data storage buckets and exploiting content security policy to transmit data to a Google Analytics account under their control.
Using Steganography to Hide Skimmer Code in EXIF
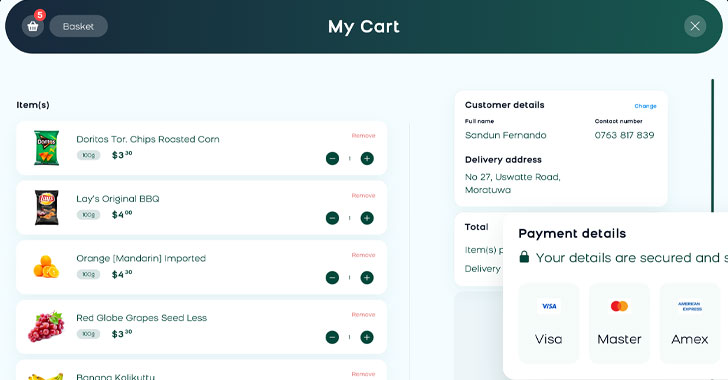
Banking on the growing trend of online shopping, these attacks typically work by inserting malicious code into a compromised site, which surreptitiously harvests and sends user-entered data to a…
http://feedproxy.google.com/~r/TheHackersNews/~3/yB7tsRWZeYw/image-credit-card-skimmers.html