Cybersecurity researcher Mordechai Guri from Israel’s Ben Gurion University of the Negev recently demonstrated a new kind of malware that could be used to covertly steal highly sensitive data from air-gapped and audio-gapped systems using a novel acoustic quirk in power supply units that come with modern computing devices.
Dubbed ‘POWER-SUPPLaY,’ the latest research builds on a series of techniques leveraging electromagnetic, acoustic, thermal, optical covert channels, and even power cables to exfiltrate data from non-networked computers.
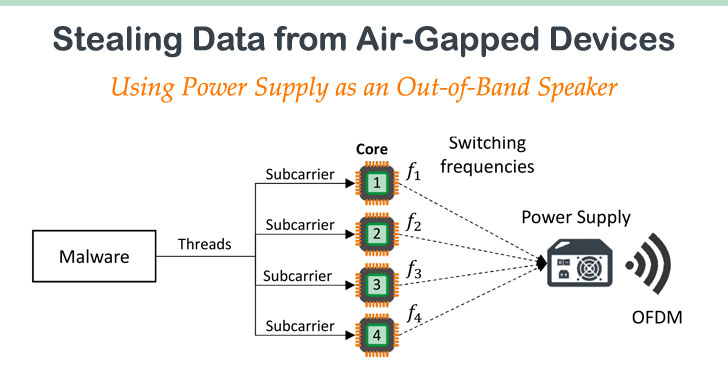
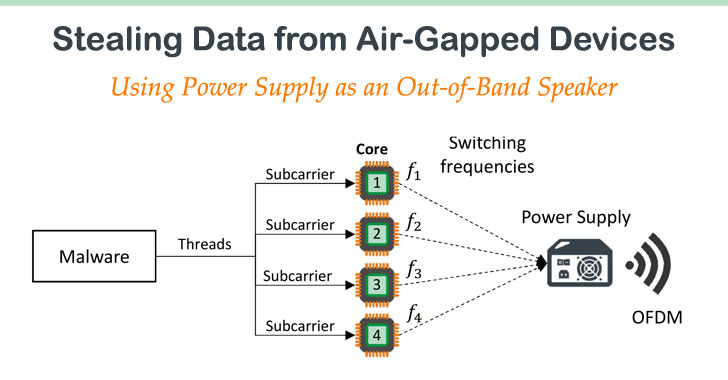
“Our developed malware can exploit the computer power supply unit (PSU) to play sounds and use it as an out-of-band, secondary speaker with limited capabilities,” Dr. Guri outlined in a paper published today and shared with The Hacker News.
“The malicious code manipulates the internal switching frequency of the power supply and hence controls the sound waveforms generated from its capacitors and transformers.”
“We show that our technique works with various types of systems: PC workstations and servers, as well as embedded systems and IoT devices that have no audio hardware. Binary data can be modulated and transmitted out via the acoustic…
http://feedproxy.google.com/~r/TheHackersNews/~3/rxbVwJaSMNE/air-gap-malware-power-speaker.html