Multiple zero-day vulnerabilities in digital video recorders (DVRs) for surveillance systems manufactured by Taiwan-based LILIN have been exploited by botnet operators to infect and co-opt vulnerable devices into a family of denial-of-service bots.
The findings come from Chinese security firm Qihoo 360’s Netlab team, who say different attack groups have been using LILIN DVR zero-day vulnerabilities to spread Chalubo, FBot, and Moobot botnets at least since August 30, 2019.
Netlab researchers said they reached out to LILIN on January 19, 2020, although it wasn’t until a month later the vendor released a firmware update (2.0b60_20200207) addressing the vulnerabilities.
The development comes as IoT devices are increasingly being used as an attack surface to launch DDoS attacks and as proxies to engage in various forms of cybercrime.
What Are the LILIN Zero-Days About?
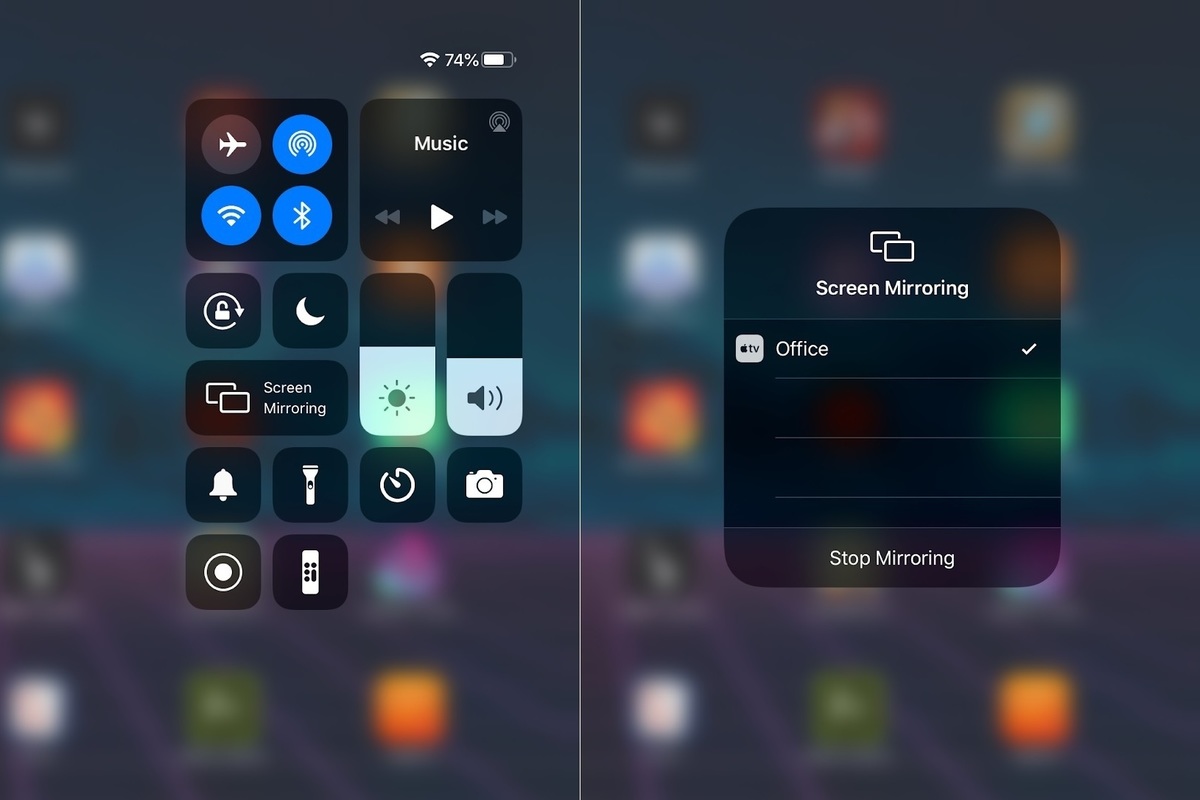
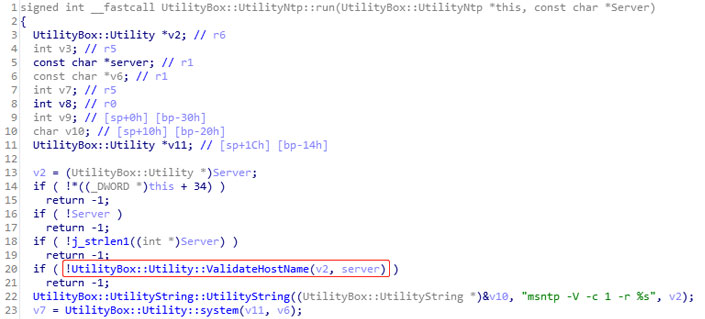
The flaw in itself concerns a chain of vulnerabilities that make use of hard-coded login credentials (root/icatch99 and report/8Jg0SR8K50), potentially granting an attacker the ability to modify a DVR’s configuration file and inject backdoor commands when the FTP or NTP server configurations are synchronized.
In…
http://feedproxy.google.com/~r/TheHackersNews/~3/TrfteovCQsw/ddos-botnets-lilin-dvr.html