Attention Linux Users!
A vulnerability has been discovered in Sudo—one of the most important, powerful, and commonly used utilities that comes as a core command installed on almost every UNIX and Linux-based operating system.
The vulnerability in question is a sudo security policy bypass issue that could allow a malicious user or a program to execute arbitrary commands as root on a targeted Linux system even when the “sudoers configuration” explicitly disallows the root access.
Sudo, stands for “superuser do,” is a system command that allows a user to run applications or commands with the privileges of a different user without switching environments—most often, for running commands as the root user.
By default on most Linux distributions, the ALL keyword in RunAs specification in /etc/sudoers file, as shown in the screenshot, allows all users in the admin or sudo groups to run any command as any valid user on the system.
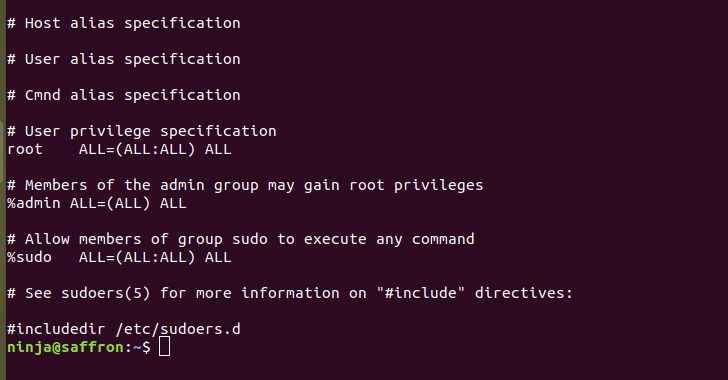
However, since privilege separation is one of the fundamental security paradigms in Linux, administrators can configure a sudoers file to define which users can run what commands as to which users.
So, even if a user has been restricted to run a specific, or…
http://feedproxy.google.com/~r/TheHackersNews/~3/_zTbOwZXHSo/linux-sudo-run-as-root-flaw.html












